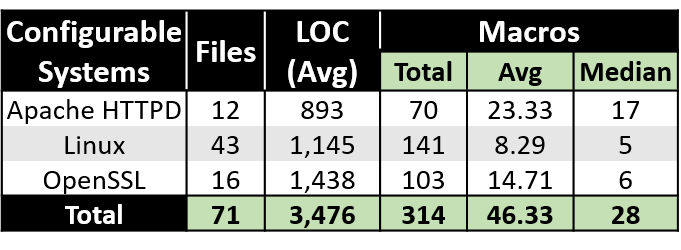
Table 1: Configurable systems analyzed in our study. LOC(Avg) = Average of lines of code; Total = Total of macros; Avg = Average of macros; Median = Median of macros.
Raphael Muniz, Rohit Gheyi, Larissa Braz, Wilkerson Andrade, Baldoino Fonseca, Márcio Ribeiro
Abstract
A number of critical configurable systems are implemented using #ifdefs, such as Linux. Some tools and strategies are proposed to avoid them. However, these systems still have weaknesses, leading to vulnerable code, and may impact millions of users. There is a lack of studies regarding the perception of developers of configurable systems with #ifdefs related to weaknesses, and the strategies and tools they use to remove them. Moreover, few works study the characteristics of weaknesses. To better understand the problem, we conduct two studies. In the first one, we qualitatively analyze 29 variability weaknesses of Apache HTTPD, Linux and OpenSSL reported on their bug trackers. In the second study, we conduct a survey with 110 developers of the previous configurable systems. Overall, our results show evidences that, although developers care about weaknesses, they may not detect some weaknesses reported in the bug trackers, and do not use proper tools to deal with them. They take on median 15 days and 4 discussion messages to solve them. Some weaknesses occur due to two or three feature interactions, and most of them can be detected by the all macros enabled sampling approach.
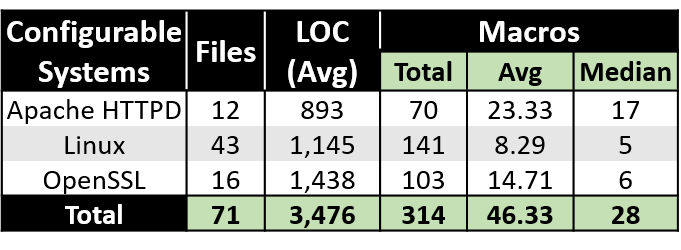
Table 1: Configurable systems analyzed in our study. LOC(Avg) = Average of lines of code; Total = Total of macros; Avg = Average of macros; Median = Median of macros.
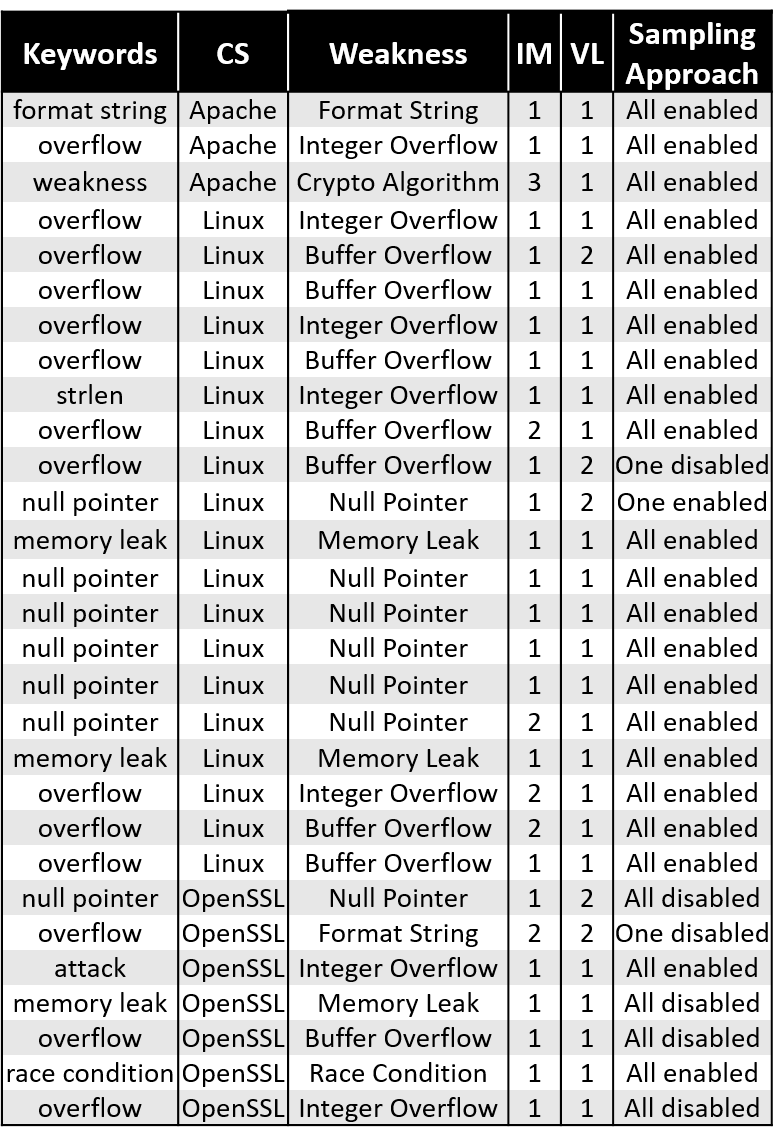
Table 2: Analyzed Variability Weaknesses. CS = Configurable Systems; IM = Involved Macros; VL = Variability Level.
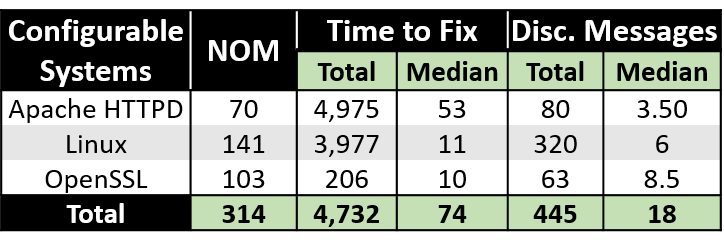
Table 3: Median and total of time and discussion messagesto fix a variability weakness per analyzed configurable systems. NOM = Number Of Macros; Disc. Messages = Discussion Messages.
(a) Weakness in option “A”.
(b) Weakness in option “B”.
(c) Weakness in option “B”.
(d) Weakness in option “A”.
(e) Weakness in option “B”.
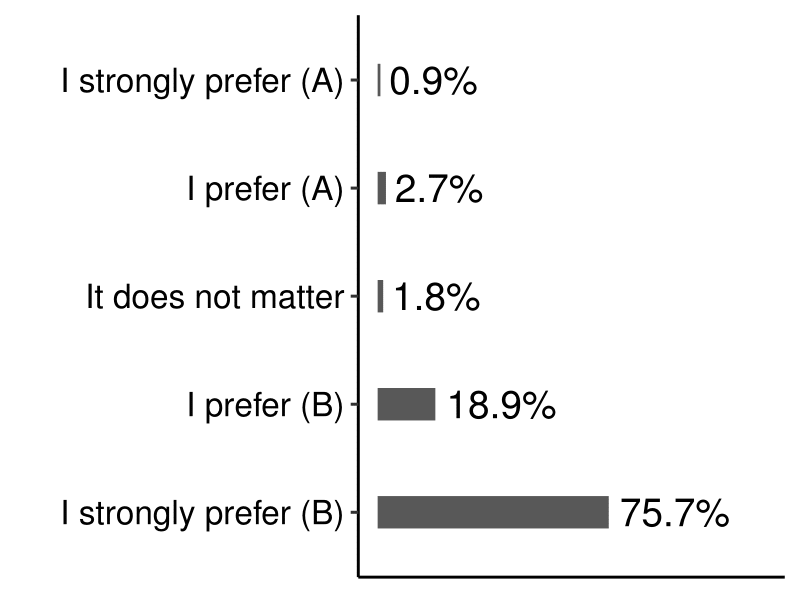
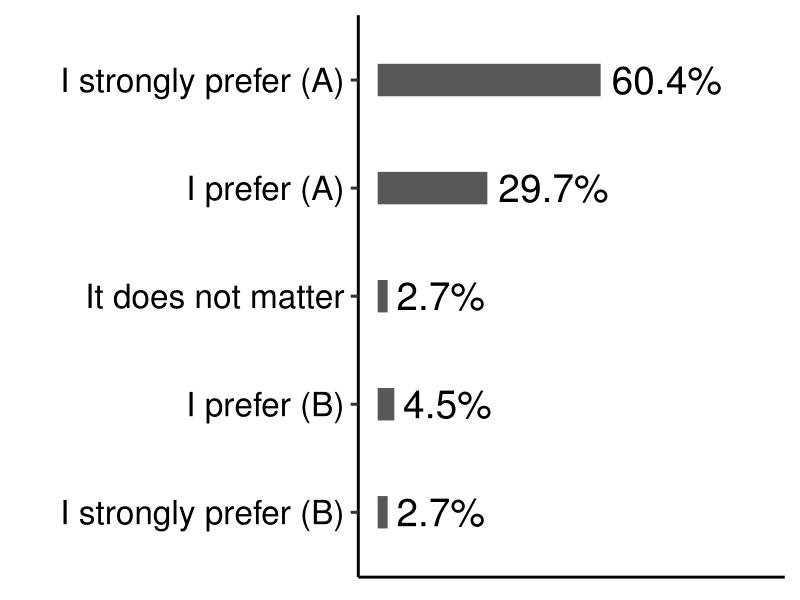
(a) How much do you care about weaknesses when performing a commit?
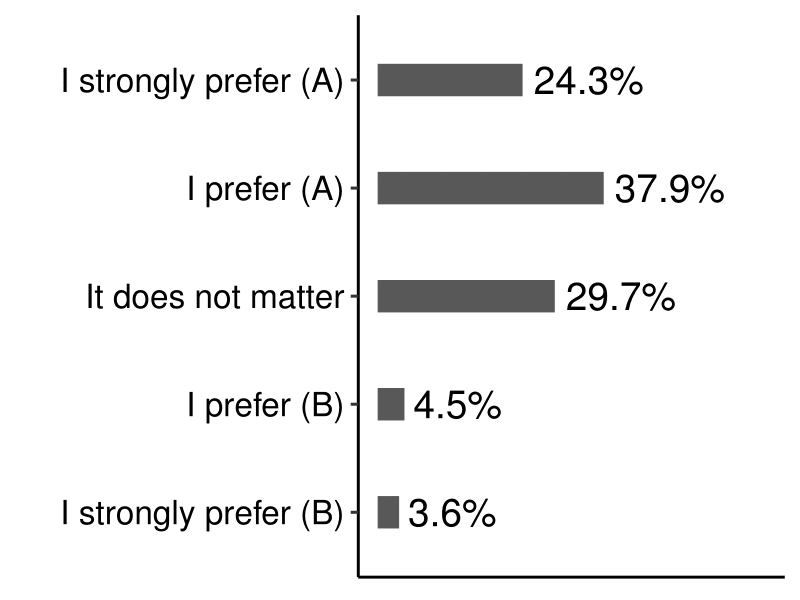
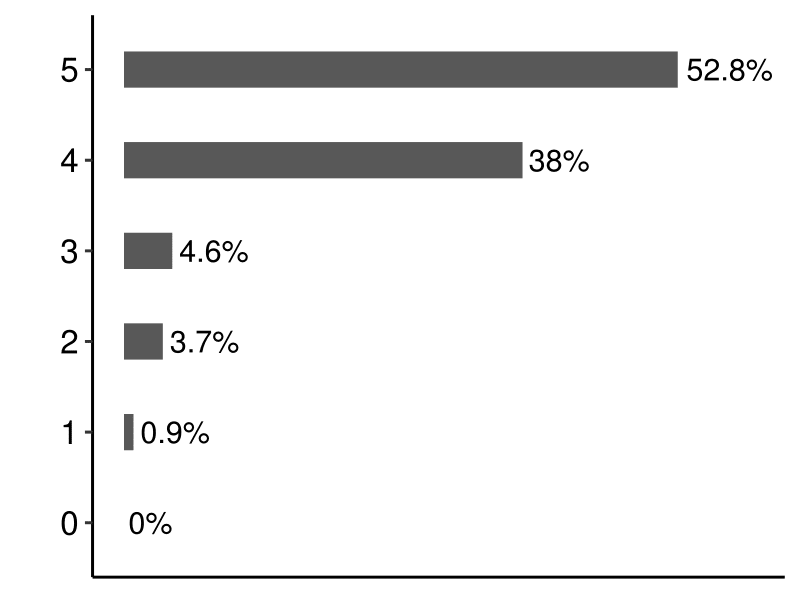
(b) What is your background/knowledge about weaknesses in configurable systems with #ifdefs?
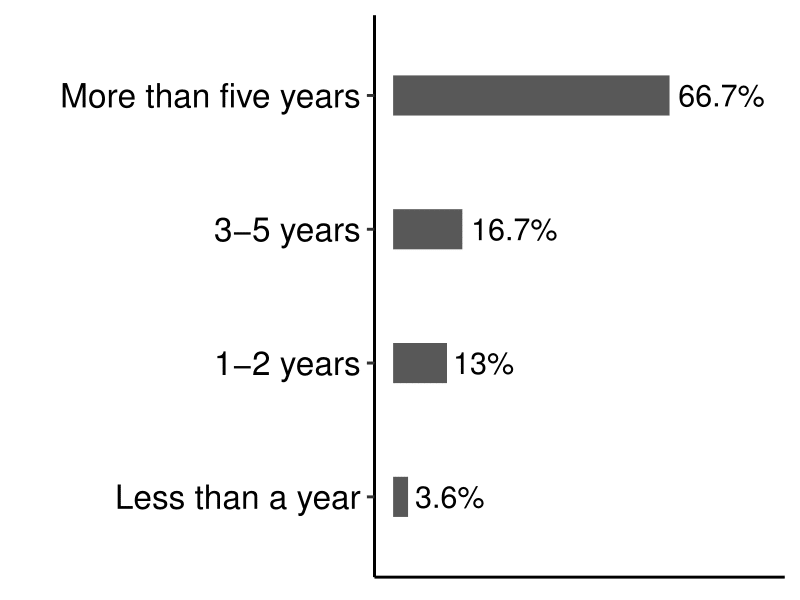
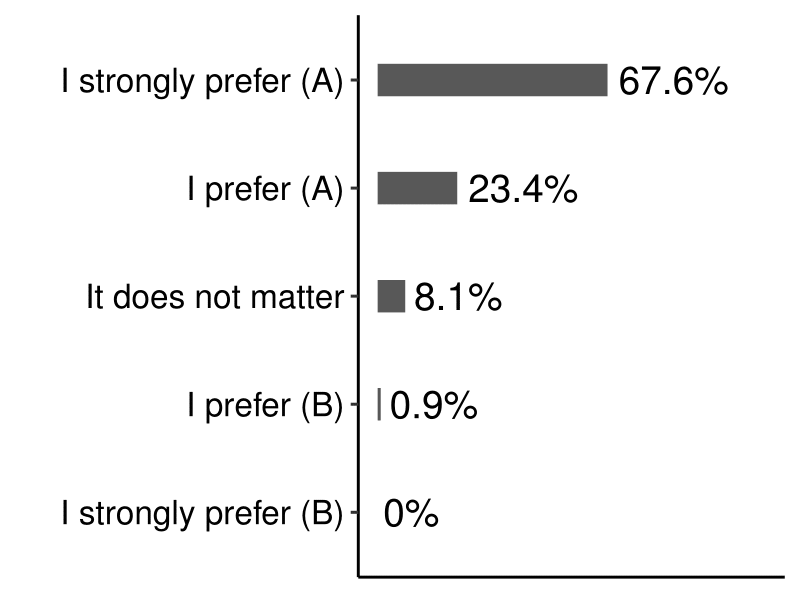
(c) For how long have you been working/have worked with preprocessor directives #ifdefs?
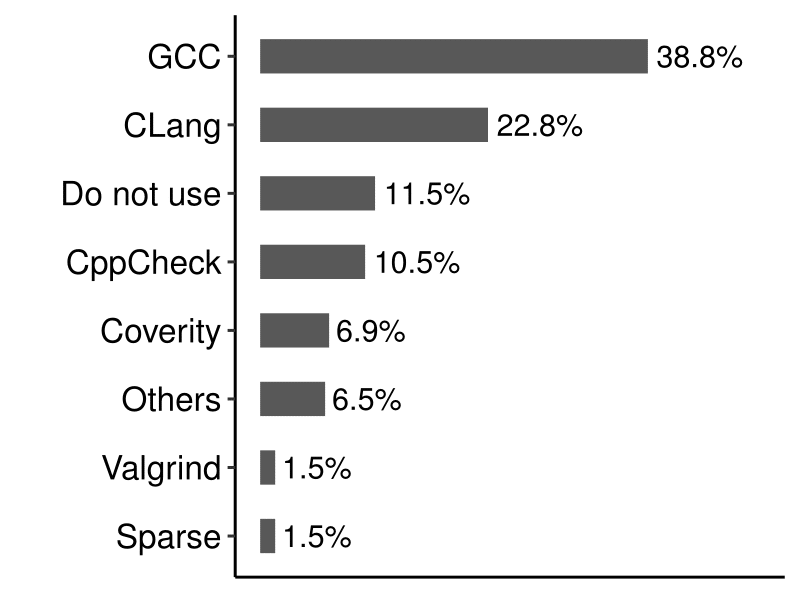
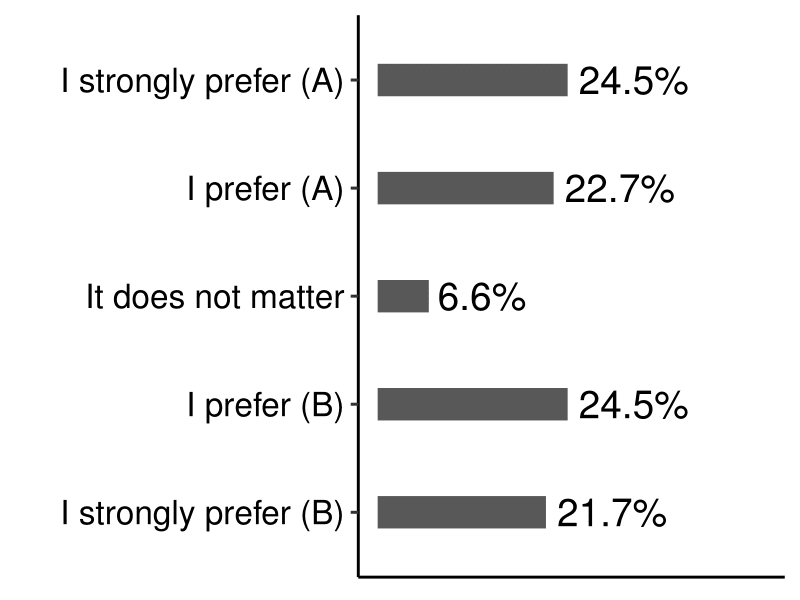
(d) Do you use any tool(s) to detect weaknesses in the code? Which one(s)?
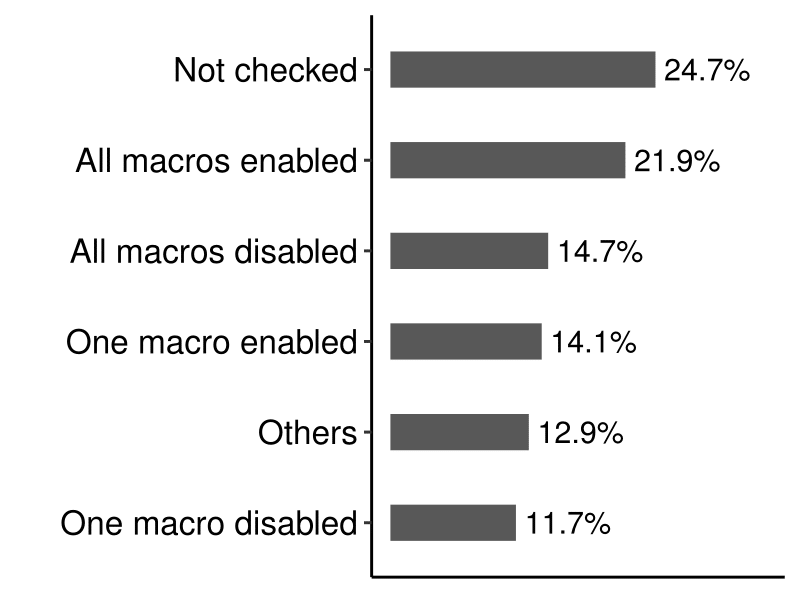
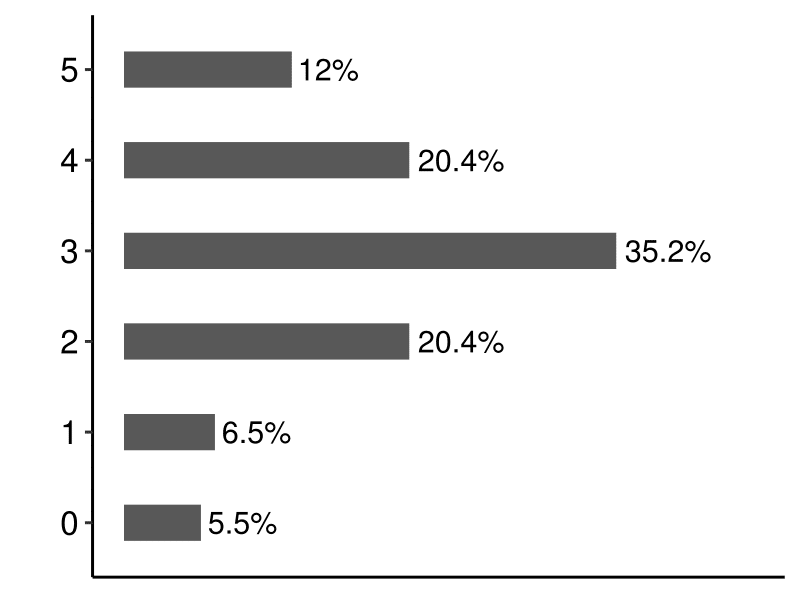
(e) When you verify the presence ofbugs/weaknesses in the code, whichconfigurations do you usually check?